TO: Board of Directors; Chief Executive Officers
DATE: April 27, 2026
SUBJECT: Structural Shifts in Cyber Liability and Insurability
- INTRODUCTION: THE PROPHETIC REALITY
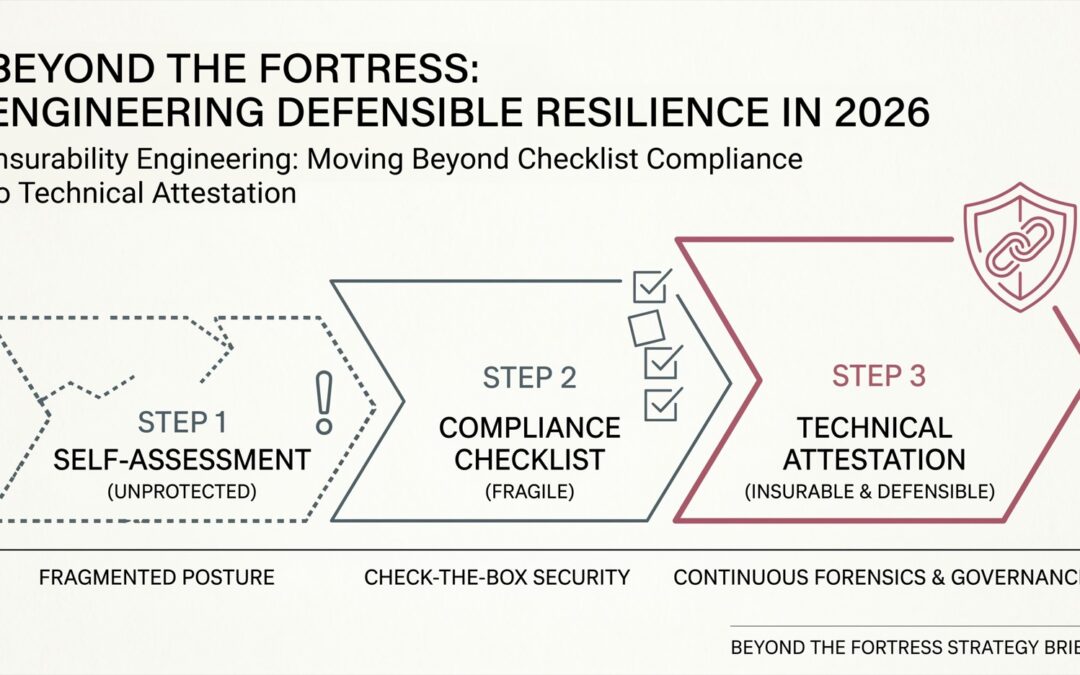
As of mid-2026, the traditional cybersecurity paradigm has shifted from a “protective fortress” model to one of technical attestation and assumed breach. For decades, organizations invested in perimeter defenses under the assumption that high walls ensured safety. However, the maturation of industrialized campaigns—such as those attributed to Salt Typhoon [1]—has demonstrated that even well-defended and critical infrastructure environments are vulnerable to persistent, “gray zone” intrusions.
We have entered an era where your organization will no longer be judged solely by the strength of the walls you built, but by the quality, completeness, and integrity of the evidence you can produce when those walls are bypassed.
- EXECUTIVE REALITY CHECK
Leadership teams must acknowledge four structural truths shaping the 2026 risk landscape:
- Perimeter Degradation: Identity-based attacks (vishing, credential harvesting, session hijacking) routinely bypass traditional and next-generation perimeter controls.
- Industrialized Adversaries: Modern threat actors operate with the scale of an enterprise, combining automation, specialization, and global coordination.
- Process Over Product: High-impact incidents frequently originate from breakdowns in operational process (identity verification, access control, escalation paths) rather than novel technical exploits.
- The Telemetry Mandate: Incident response is now an evidence-driven discipline. Without sufficient, retained, and integrity-protected telemetry, insurance claims, regulatory responses, and legal defensibility are materially weakened.
III. THE PARADOX OF THE “HEAVY LIFTING”
Modern cyber threats scale at machine speed, leveraging automation and increasingly AI-assisted reconnaissance and lateral movement. This complexity creates a dangerous psychological trap: the assumption that cybersecurity is exclusively the domain of specialists or external entities.
Private organizations are now active participants in a contested digital environment. The 2023 breach of MGM Resorts International [2] serves as a landmark example. Attackers gained initial access through a brief social engineering interaction with a help desk. The result was an estimated $100 million operational impact [3] within a single quarter.
This reinforces a critical point: organizations are rarely compromised by “unstoppable” attacks alone, but by exploitable process gaps that no external party can fully mitigate on their behalf.
- LEADERSHIP RESPONSIBILITY: THE DRIVING ANALOGY
A persistent barrier to executive engagement is the “Expertise Excuse”—the belief that technical depth is required to lead security strategy.
Consider a high-performance vehicle. Ownership does not require mechanical expertise; it requires ensuring that maintenance occurs, records are preserved, and risks are managed responsibly. Cybersecurity leadership follows the same model. Delegation is necessary—but failure to ensure verifiable operational records increasingly constitutes a fiduciary and governance risk.
- THE NEW STANDARD: DEFENSIBLE EVIDENCE
In a breach-normalized environment, “best effort” is no longer a sufficient legal or financial position. A defining example emerged during the 2023 Microsoft Storm-0558 intrusion [4], where the Cyber Safety Review Board (CSRB) [5] noted that investigation and detection were significantly constrained by limited audit logging availability.
In response, industry guidance—such as NIST SP 800-92 [6]—along with evolving cyber insurance underwriting practices, increasingly emphasize the retention of meaningful security telemetry. A commonly observed benchmark is approximately 90 days of accessible, high-integrity telemetry, though specific requirements vary by insurer and regulatory context.
Organizations unable to produce sufficient telemetry to reconstruct security events may face challenges demonstrating that appropriate controls were in place and functioning.
- FIELD OBSERVATIONS: LESSONS IN PRESERVATION
The importance of telemetry preservation was clearly illustrated following the 2020 SolarWinds supply-chain compromise [7], where investigators faced significant challenges reconstructing timelines due to incomplete or unavailable logging data [8].
Aggregated breach data continues to reinforce consistent patterns. Identity remains a primary attack vector, with a majority of breaches involving some form of credential compromise [9]. Median dwell times frequently extend for weeks or longer, depending on detection maturity [10].
In this environment, operating without a verifiable security history—records demonstrating system activity, control enforcement, and response actions—creates both operational and financial exposure.
VII. THREE QUESTIONS FOR THE BOARD
- Could our organization reconstruct a defensible breach timeline within applicable regulatory notification windows (e.g., California disclosure requirements)?
- Is our security telemetry retained with sufficient duration, integrity, and protection against tampering or deletion?
- Can we demonstrate insurability based on verifiable controls and evidence, rather than self-attestation alone?
REFERENCES
[1] CISA and FBI, *Joint Advisory on Chinese State‑Sponsored Cyber Activity (Salt Typhoon)*, 2024.
[2] J. Lapeyre, *The MGM Resorts Cyberattack: When Identity Becomes the Weakest Link*, 2023.
[3] MGM Resorts International, *SEC Form 8‑K: Q3 2023 Financial Impact*, 2023.
[4] Microsoft Security, *Forensic Analysis of Storm‑0558 Cloud Account Compromise*, 2023.
[5] Cyber Safety Review Board, *Review of the Summer 2023 Microsoft Online Exchange Incident*, DHS, 2024.
[6] NIST, *SP 800‑92: Guide to Computer Security Log Management (Update)*, 2024.
[7] U.S. GAO, *Federal Response to SolarWinds and Microsoft Exchange Incidents*, GAO‑22‑104746, 2022.
[8] CISA, *SolarWinds Incident: Lessons Learned and Strategic Mitigation*, 2021.
[9] Verizon, *2025 Data Breach Investigations Report*, 2025.
[10] Mandiant / CrowdStrike, *Global M‑Trends & Threat Report*, 2025.